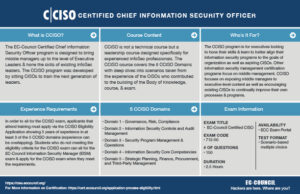
CCISO Certification
About the Program
EC-Council’s CCISO Program has certified leading information security professionals around the world. A core group of high-level information security executives, the CCISO Advisory Board, contributed by forming the foundation of the program and outlining the content that would be covered by the exam, body of knowledge, and training. Some members of the Board contributed as authors, others as exam writers, others as quality assurance checks, and still others as trainers. Each segment of the program was developed with the aspiring CISO in mind and looks to transfer the knowledge of seasoned professionals to the next generation in the areas that are most critical in the development and maintenance of a successful information security program.
The Certified CISO (CCISO) program is the first of its kind training and certification program aimed at producing top-level information security executives. The CCISO does not focus solely on technical knowledge but on the application of information security management principles from an executive management point of view. The program was developed by sitting CISOs for current and aspiring CISOs.
In order to sit for the CCISO exam and earn the certification, candidates must meet the basic CCISO requirements. Candidates who do not yet meet the CCISO requirements but are interested in information security management can pursue the EC-Council Information Security Management (EISM) certification.
Why should you consider the CCISO program?
The CCISO Certification is an industry-leading program that recognizes the real-world experience necessary to succeed at the highest executive levels of information security.Bringing together all the components required for a C-Level positions, the CCISO program combines audit management, governance, IS controls, human capital management, strategic program development, and the financial expertise vital to leading a highly successful IS program. Material in the CCISO Program assumes a high-level understanding of technical topics and doesn’t spend much time on strictly technical information, but rather on the application of technical knowledge to an information security executive’s day-to-day work. The CCISO aims to bridge the gap between the executive management knowledge that CISOs need and the technical knowledge that many aspiring CISOs have. This can be a crucial gap as a practitioner endeavors to move from mid-management to upper, executive management roles. Much of this is traditionally learned as on the job training, but the CCISO Training Program can be the key to a successful transition to the highest ranks of information security management.
The NICE Cybersecurity Workforce Framework (NCWF)(link is external) NIST Special Publication 800-181, is a national resource that categorizes and describes cybersecurity work.The NCWF provides employers, employees, educators, students, and training providers with a common language to define cybersecurity work as well as a common set of tasks and skills required to perform cybersecurity work.
EC-Council has mapped the domains of CCISO to the NCWF in the following document.
EC-Council is dedicated to working with the US Department of Defense to bring the highest standards of Training, Education and Certification to our military.
Independent Accreditation ensures Quality of Certification
EC-Council Certifications are developed to the highest standards and have achieved numerous accreditations including ANSI 17024 for:

DoD Directive 8570/ 8140
EC-Council’s Certified Ethical Hacker is an approved baseline certification for the following Cyber Security Service Provider sections:

IAM Level II • IAM Level III • CSSP Manager
Information on DoD 8570 can be found at the following DISA website:https://public.cyber.mil/cw/cwmp/dod-approved-8570-baseline-certifications/
Certification to Framework Mappings
A core component of EC-Council Certification development is the Job Task Analysis (JTA) Process we undertake before any certification is built. Major frameworks like the NICE/NIST Framework, NIST 800-171, GCHQ, and others contribute to content areas of each of our programs. As a result, EC-Council Certifications and Training programs are mapped to most major published Frameworks.
EC-Council Maps to the National Initiative for Cybersecurity Education Framework
Download the comprehensive mapping of EC-Council program sections to The Roles and their associated Knowledge, Skills and abilities.

EC-Council Cyber Security Certifications and the US NAVY
Six EC-Council Certifications are recognized by the United States Navy in over 100 Cyber Security Job roles, across 18 occupations. Ranging from Commander in Executive Cyberspace Leadership to Cyber Warfare Engineer, Special Agents, Incident Handlers, to Cryptologic Warfare Engineers, Cybersecurity careers with the US NAVY are exciting, holding an EC-Council certification provides great opportunity for advancement in a US NAVY career.
The decisions of Department of the NAVY to incorporate industry recognized certifications into the Cyber IT & Cyber Security Workforce Framework ensures as our service personnel advance their careers and eventually transition to civilian life, their skills and credentials are widely recognized by the Industries they will continue to work in as Veterans.
Certifications recognized, accepted, and often funded by the US NAVY include:

Funding opportunities for career advancement are available for Active Duty NAVY personnel through the NAVY COOL program.
US NAVY approves EC-Council Certifications across 18 Occupations and over 100 Job roles
*All information represented here can be found on the NAVY COOL site. To find what EC-Council Certifications map to your eligible Job role, select “Full Credential Search” then under Credential Agency, select or search for “International Council of E-Commerce Consultants”.

EC-Council Cyber Security Certifications and the US ARMY
Five EC-Council Certifications are recognized by the United States ARMY across 15 occupations. Ranging from Cyber Operations Technician to Target Digital Network Analyst. Our certifications are in use as baseline credentials across ARMY Cyber throughout intelligence as well as deployed infantry. EC-Council is proud to work with various groups in the ARMY to support the Mission of ARMY Cyber.
Certifications recognized, accepted, and often funded by the US ARMY include:

Funding opportunities for career advancement are available for Active Duty ARMY personnel through the ARMY COOL program.
US ARMY approves EC-Council Certifications across 15 Occupations
- Cryptologic Cyberspace Intelligence Collector - Analyst
- CYBER Operations Technician
- Information Protection Technician
- Military Intelligence (MI) Systems Maintainer/Integrator
- Senior Network Operations Technician
- Cryptologic Cyberspace Intelligence Collector - Analyst
- CYBER Operations Technician
- Information Protection Technician
- Military Intelligence (MI) Systems Maintainer/Integrator
- Senior Network Operations Technician
- Counterintelligence Agent
- Cyber Operations Specialist
- Infantryman
- Information Technology Specialist
- Nodal Network Systems Operator-Maintainer

EC-Council Cyber Security Certifications and the Marine Corps
Five EC-Council Certifications are recognized by the United States Marine Corps in 79 Cyber Security Job roles, across 17 occupations. Ranging from Cyber Security Technician, to Signals Intelligence and Electronic Warfare Operator, to Cyber Security Chief.
Certifications recognized, accepted, and often funded by the US Marine Corps include:

Funding opportunities for career advancement are available for Active Duty MARINE CORPS personnel through the Marine COOL program.
US ARMY approves EC-Council Certifications across 15 Occupations

EC-Council Cyber Security Certifications and the US Air Force
Four EC-Council Certifications are recognized by the United States Air Force in 150 Cyber Security Job roles, across 8 occupations. Occupations are recognized in fields like; Cyber Transport Systems, Intelligence, and Cyber Warfare Operations.
Certifications recognized, accepted, and often funded by the US AIR FORCE include:

Funding opportunities for career advancement are available for Active Duty AIR FORCE personnel through the AIR FORCE COOL program.
Use the links below to navigate the certification process: